
- Darren Thomson
Industrial Control Systems & Connections to the Wild Internet – It Appears That Lessons Are Not Being Learned
News broke this week of a ransomware attack bringing an unnamed US gas pipeline facility to its knees.
Read Article

.png)
- Laurel Di Silvestro
Silent Cyber and the Role of Data in Modeling
Silent cyber exposure is now up front and center in every discussion topic for non-property lines of business, and increasingly for property as well
Read Article

.png)
- John Anderson
Reflections for the UK Broker Market 2020
Cyber insurance was brought up at the party as one such area for growth, citing an 11% penetration of UK companies having some form of cyber coverage.
Read Article

.png)
- Oliver Brew
CyberCube 2020 Summit and Hackathon!
The whole of CyberCube got together in San Francisco for our 2020 planning meeting as well as a new company first: a Hackathon.
Read Article

- Pascal Millaire
Davos: 6 takeaways and 1 overarching theme
Pascal Millaire shares his 6 takeaways from the World Economic Forum's 2020 Davos Conference.
Read Article


- Pascal Millaire
Cybersecurity at Davos: Is there anything we can agree on?
Reaching alignment within a country and industry on cyber issues is a tough task, made harder when you broaden the stakeholders as the WEF aspires to do.
Read Article

.png)
- Nick Beecroft
Travelex attack highlights increasing ransomware threat to large enterprises
Weeks on from the ransomware attack which crippled systems at Travelex, the foreign exchange firm continues to suffer disruption to its business.
Read Article


- Alejandro Sauter
Data Theft: Passing Trend or Permanent Add to Ransomware?
This year we observed the bear’s share of the ransomware market consisting of 2 main approaches: the ransomware-as-a-service (RaaS) & the big game hunting
Read Article


- Ashwin Kashyap
Models must evolve to tackle silent cyber
Insurers are finding themselves squeezed between regulators and reinsurers who both want the issue of so-called ‘silent cyber’ risk to be tackled.
Read Article

- Emmanuel Thioux
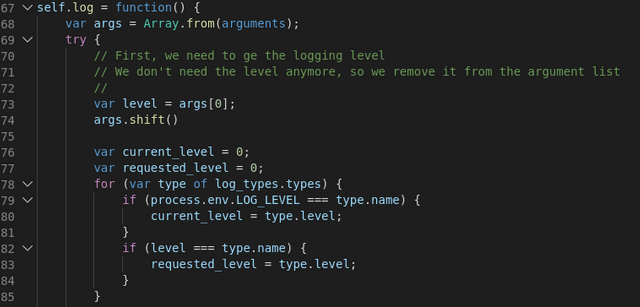
Technology Series: Improving logging in Lambda functions
How to improve logging and store the logs into external systems, such as Kibana.
Read Article


- Yvette Essen
CyberCube's analysis of the Amazon Web Services outage enables a greater understanding of the evolution of cyber threats
Analysis of the technical aspects of AWS denial of service attack and its potential implications on insurers' portfolios.
Read Article


- Rebecca Bole
Inter-disciplinary coordination required to tackle cyber risk: Science Magazine
Bringing diverse perspectives into a team to tackle some of the most complex risks facing society today is imperative
Read Article
