Cyber Threat Intelligence
- William Altman
Cyber catastrophe meets enterprise ransomware: Colonial Pipeline attack
Cyber criminal gangs are targeting single-point-of-failure technologies and CyberCube can help (re)insurers both identify key SPoF-related cyber risks and model threats to SPoF technologies and companies.
Read Article

.png)
- William Altman
Three cyber insurance takeaways from the OVHCloud fire
The OVHCloud data center fire highlights important lessons for cyber insurers
Read Article


- Darren Thomson
Advances in social engineering technology (and why we should care)
Social engineering is not new but recent developments in this area leverage AI to make techniques all the more powerful and dangerous.
Read Article


- Alejandro Sauter
Analyzing the footprint of recent Chrome and Windows zero-days discovery
Palo Alto Networks said “80% of exploits publish faster than CVEs” in August. We are facing this with two new zero-days being exploited in the wild in the most popular browser and OS in the world. Here we will explore the proportion of impacted networks and if any of them are quick to react (i.e. patch).
Read Article


- Darren Thomson
Another Cloud Outage – Are We Headed For “The Big One”?
AWS customers experienced another service outage last week as an apparently non-malicious incident took services down for around 8 hours.
Read Article

.jpg)
- Darren Thomson
Enterprise Ransomware: To Pay or Not to Pay… Is that even the question?
Paying ransoms to cybercriminals may not continue to be an option to legitimate businesses as the US government warns of penalties for organizations who fund criminal gangs
Read Article

.png)
- Wenfeng Yan
More Cloudy, Less Chance of Data Breach?
CyberCube's cyber data correlation analysis shows that more cloud adoptions are not automatically guaranteed less data breach incidents.
Read Article


- Darren Thomson
Automation in cyber crime – A key enabler of future risk accumulation?
Automation and associated technologies could lead to more frequent risk accumulation events.
Read Article


- Charlotte Anderson
Attack Vector Deep Dive: Mobile Attacks
The main types of cyber attacks on mobile devices
Read Article

- Mohammad Al Boni
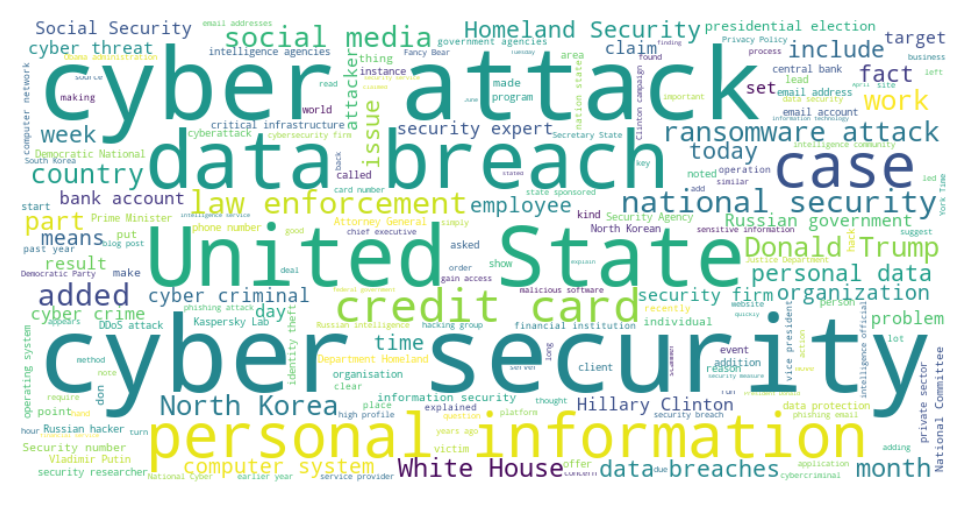
CyberTrends: Extracting Insights from news articles
Machine Learning, Text Analysis, Cyber News, Correlation Analysis, Topic Modeling, Document Embeddings
Read Article


- Charlotte Anderson
Attack Vector Deep Dive: Exposed Databases
This blog discusses the main types of attacks that occur on exposed databases, and important security steps toward protecting enterprises from this risk.
Read Article


- Darren Thomson
Ransomware and the “Double-Dipping” Trend
A recent trend in enterprise ransomware sees criminals making not one, but two financial demands
Read Article
