The rise of "cryptojacking" has been a major trend in the cyber threat landscape since 2017, but the associated risk of business disruption is low. Publicly-reported incidents, such as the cyber operation against the Japanese lens-maker Hoya Corp. which involved (attempted) cryptojacking and resulted in production delays, are the extreme exception rather than the norm.
At its core, cryptojacking refers to the abuse of computer resources to mine cryptocurrency. The most prevalent form involves browser resources being hijacked by a script on a visited website. A more dangerous and lucrative version is file-based cryptojacking, where adversaries manage to load a file on personal or corporate computers. Finally, there have been isolated cases of cryptojacking software being deployed to entire networks to mine cryptocurrency on hundreds or thousands of systems.
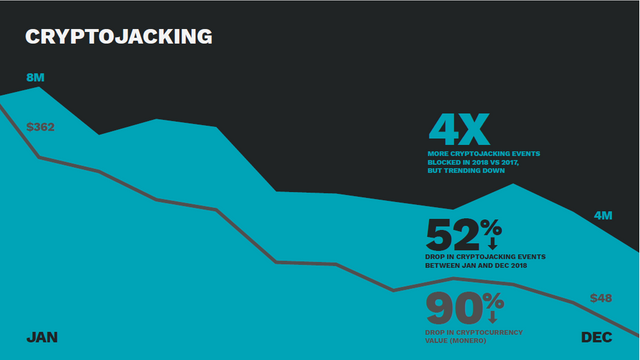
CyberCube’s strategic partner, Symantec, assessed in its annual Internet Security Threat Report that cryptojacking is “trending down, but certainly not out”. The world’s largest cyber security company blocked 8 million cryptojacking attempts in January 2018, compared to 3.5 million in December. However, Symantec only reports one case where a South American automaker was breached and cryptominers were loaded onto thousands of systems; the vast majority is browser-based or file-based activity against individual users.
It’s possible that some cyber threat actors are experimenting with network intrusions and large-scale cryptominer deployment, like the “big game hunting” trend in ransomware. However, the attraction of cryptojacking is its subtlety and adversaries benefit monetarily from staying unnoticed for longer periods of time. Cases of business disruption have been few and far between, and are likely to remain so.

.png)
